Microsoft 365 Copilot: Enterprise Guide (2026)
Lire l'article[NEW] MYDATAMANAGEMENT TO CLEAN UP YOUR OBSOLETE, UNUSED AND VOLUMINOUS DATA
Solutions
Effective response to six major challenges in data security
#1 user-interacting platform for detection
Discover the platform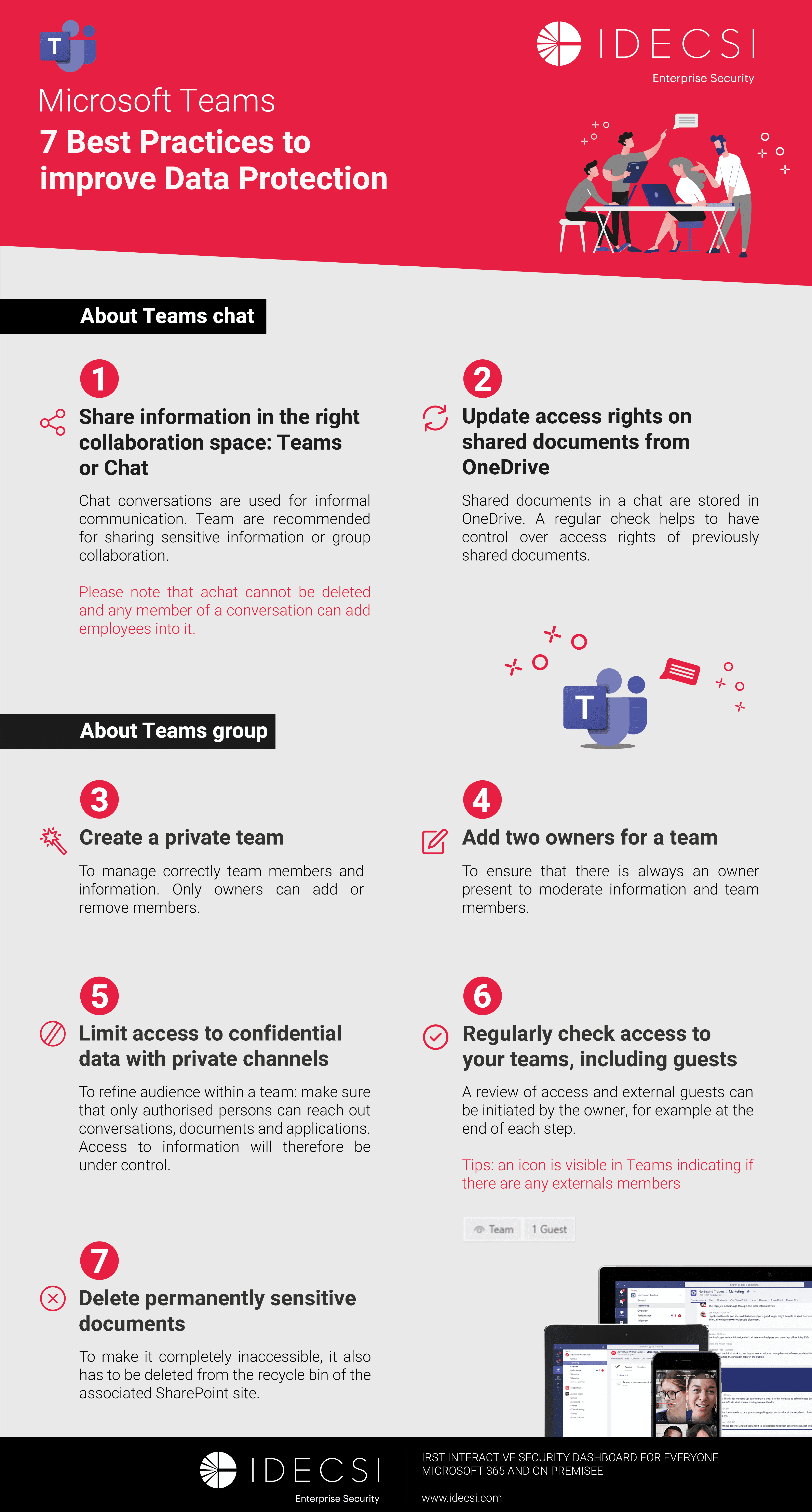
Best practices to improve Microsoft Teams security
Download the infographicOur resources
Check out our useful resources for improving data protection
Microsoft 365
10 December 2021

Data security has become a race against time. Between the explosion in data volumes (+30% per year on average), multicloud dispersion, and the massive adoption of generative AI like Microsoft 365 Copilot, the attack surface of organizations has considerably expanded.
IT and Security teams can no longer simply build walls around the perimeter. The central challenge of 2026 is Data Security Posture Management (DSPM): knowing where sensitive data is located, who accesses it, and how it is protected.
2026 Update: What's New in Microsoft Purview?
The Microsoft security ecosystem has evolved. Microsoft Purview is now a unified platform bringing together governance, compliance, and protection.
Data breaches, whether accidental (internal negligence) or malicious (exfiltration), represent a major financial and reputational risk. With GDPR and new directives (NIS2, DORA), data traceability is no longer optional.
But a new risk has emerged: governance debt. Millions of unclassified, obsolete, or "ROT" (Redundant, Obsolete, Trivial) files accumulate. Without classification, sensitive data (PII, patents, strategy) is treated as public data.
To transform this chaos into secure capital, the recommended method follows a progressive logic:
Before protecting, you must know. Data inventory (Data Discovery) answers key questions:
It is crucial to define a classification framework that is simple and understandable by everyone. Too many levels kill adoption. The market standard has stabilized around 4 levels:
This is the heart of the system. Applying a Sensitivity Label anchors classification in the file's metadata.
This label follows the data wherever it goes, even if it leaves the Microsoft 365 environment (but their application/encryption outside M365 depends on client support, e.g., Adobe PDF may not recognize labels. Protection may be lost on certain formats/platforms).
The label drives protection. Unlike past methods, we don't encrypt everything blindly.
Note: These protections are configurable by the administrator, not automatic. A "Confidential" label may have no technical protection if the admin has not configured it.
Once labeled, data becomes traceable. DLP (Data Loss Prevention) policies can then block the exit of a "Confidential" document to a USB drive or personal Gmail address.
Microsoft Purview is not just a tool, but a complete governance suite. The Information Protection module (formerly MIP/AIP) is the component dedicated to classification and encryption.
Purview Information Protection now covers the entire data lifecycle:
Access to features depends on your Microsoft 365 license level. This is a budgetary consideration:
(Note: Some advanced features require additional E5 Compliance or E5 Information Protection & Governance modules).
Microsoft Purview Information Protection (MIP) enables you to classify and label documents and emails to protect your organization's sensitive data. Data identification and classification can be performed in two ways: manually by users or automatically through predefined rules.
Manual labeling is available in all Microsoft 365 licenses (including E3, Business Premium, etc.). Users can select the appropriate sensitivity label directly from their Office applications (Word, Excel, PowerPoint, Outlook).
When a label is applied:
Some organizations configure a default label to encourage classification at document creation. The user can then modify this label according to the actual sensitivity level of the content, unless a mandatory labeling policy is in place.
The Microsoft Purview unified scanner enables automatic detection and classification of sensitive data stored on-premises (Windows file shares, SharePoint Server on-premises, etc.).
The scanner analyzes document content using:
Upon completion of the analysis, the scanner can:
Using the Microsoft Purview unified scanner requires one of the following licenses:
Technical prerequisites:
Important: The scanner is a powerful tool but requires precise configuration (content profile settings, classification rules, exception management) to avoid false positives and optimize scanning performance.
When a sensitivity label configured for encryption is applied to a document or email, Microsoft Purview Information Protection uses the Azure Rights Management (Azure RMS) service to protect the content.
Azure RMS applies AES 256-bit encryption to the entire file content, not just the metadata. The process works as follows:
Azure RMS establishes granular access control policies based on user identity:
Rights may include:
Key point: Even when a document encrypted by Azure RMS is shared with a person outside the organization, protection remains active.
This persistent file-level protection ensures that sensitive data remains secure throughout its lifecycle, regardless of the sharing channels used (email, public cloud, physical media, etc.).
Despite automation through AI, technology cannot solve everything. 80% of unstructured data requires business context to be properly qualified. The user remains the strong link if properly equipped.
The sensitivity label materializes the document's value for the user. When an employee sees a red "Highly Confidential" bar in their email, their behavior changes (increased vigilance).
Best Practices to Disseminate
While Microsoft Purview provides the infrastructure for classification and protection, companies often encounter an "operational gap": how to ensure that labels are properly applied and that permissions remain consistent over time?
This is where IDECSI comes in with native complementarity to Microsoft 365.
Visibility Focused on Real Risk
IDECSI ingests unified logs and Purview sensitivity labels to offer a consolidated view:
Microsoft admin consoles are designed for IT experts, not for business users.
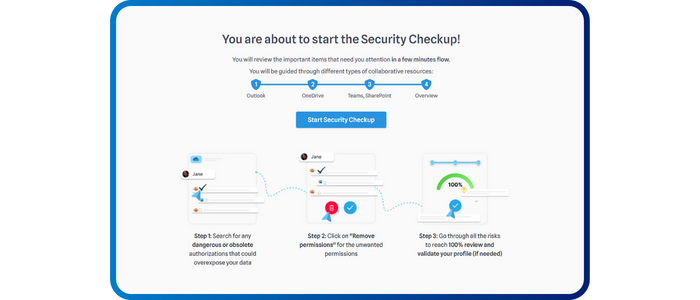
With MyDataSecurity, IDECSI directly notifies the Data Owner in case of an anomaly on a classified file:
This approach enables real-time permission correction, reduces false positives for the SOC, and maintains data hygiene essential for compliance and AI effectiveness.
Recent articles
Subscribe to our newsletter and receive new contents every month
Our articles
These articles may
interest you