OneDrive for Business Security: 3 Key Areas to Watch
Lire l'article[NEW] MYDATAMANAGEMENT TO CLEAN UP YOUR OBSOLETE, UNUSED AND VOLUMINOUS DATA
Solutions
Effective response to six major challenges in data security
#1 user-interacting platform for detection
Discover the platform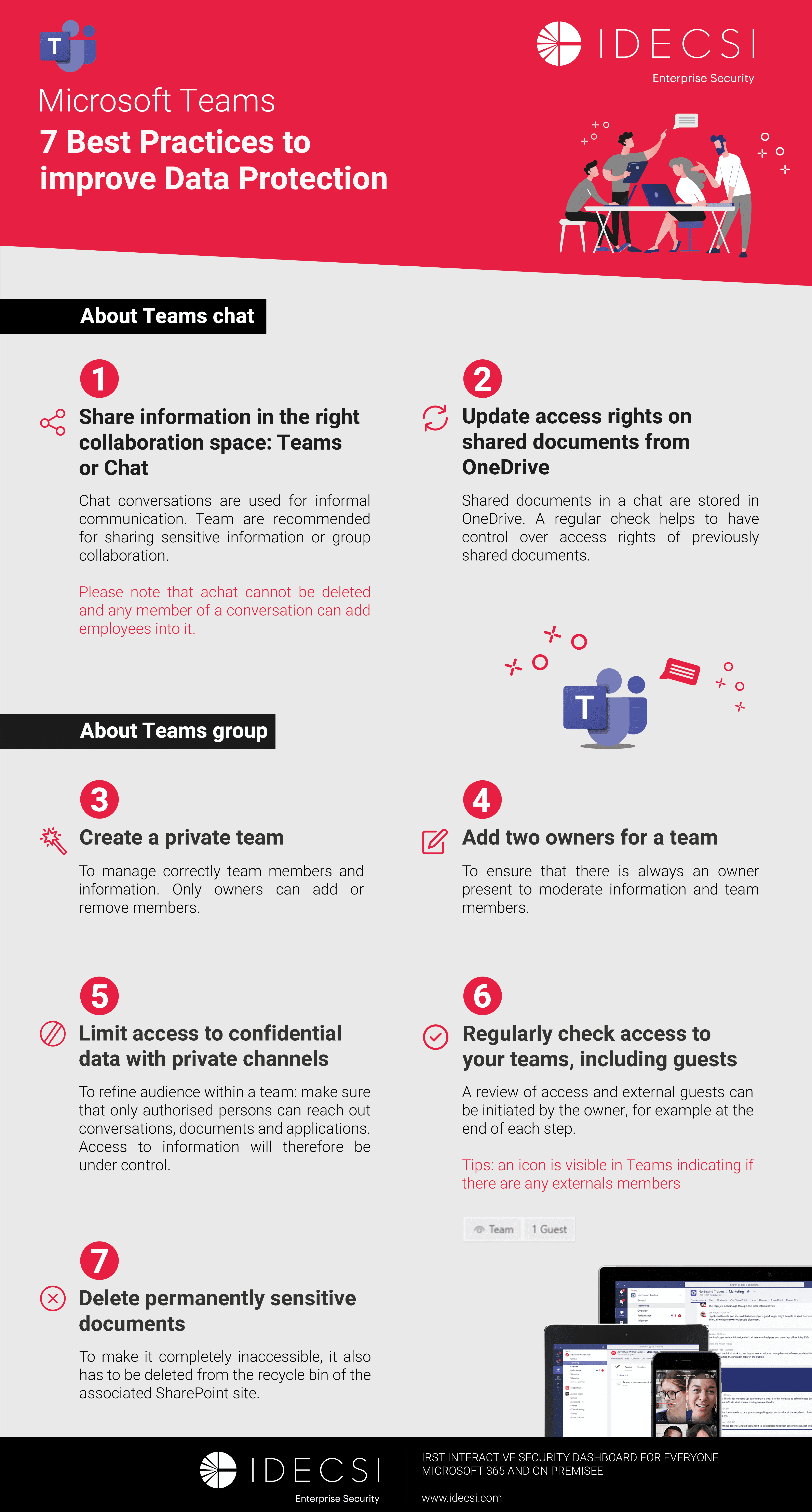
Best practices to improve Microsoft Teams security
Download the infographicOur resources
Check out our useful resources for improving data protection
Microsoft 365
21 April 2026
External sharing in Microsoft 365 is the engine of modern collaboration. It allows employees to work seamlessly with partners, clients, and vendors without leaving their work environment.
But that ease of use can quickly become a serious risk if left ungoverned. The accumulation of access links and external guests creates an attack surface that is often invisible to IT teams.
One figure puts this into perspective: at one of our clients (roughly 3,000 users), we identified more than 35,330 active anonymous links on OneDrive for Business alone. Each one of those links is a door potentially left open to your data.
Here is how to secure external sharing without blocking productivity.
2026 update: This guide incorporates the latest changes to SharePoint and OneDrive sharing options, as well as the standardization of shared channels (Teams Connect) for secure B2B collaboration.
What this article covers:
Before diving into tools and controls, it is critical to distinguish between the two core mechanisms for external sharing in Microsoft 365.
The external user is invited via their professional email address. A "Guest" account is created in your Microsoft Entra ID directory (formerly Azure AD).
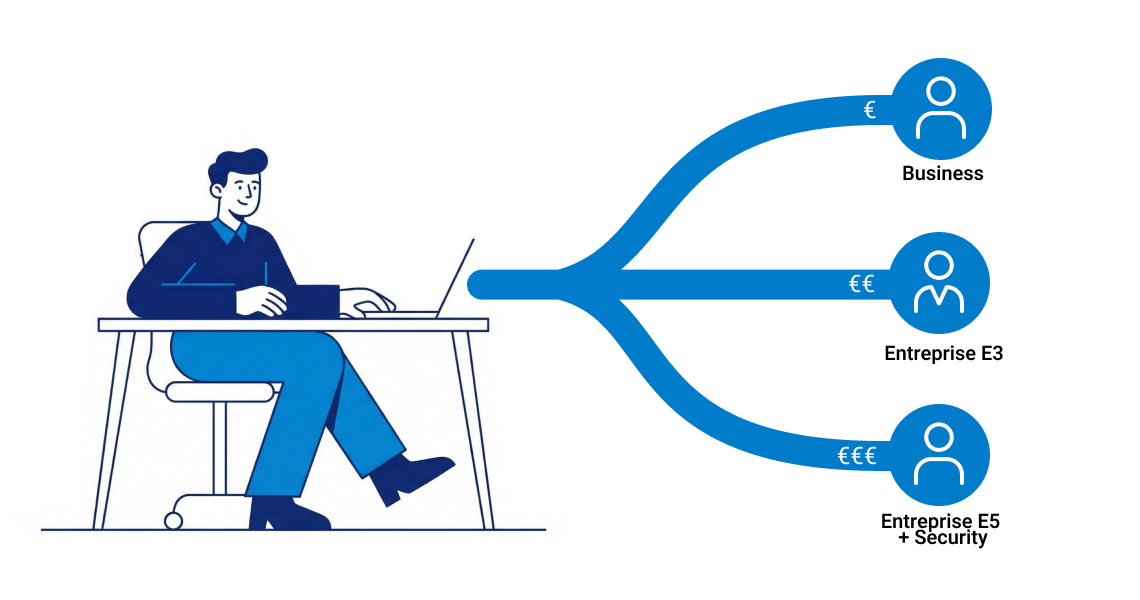
Microsoft 365 offers four types of sharing links, ranked from most to least secure.
Security reminder: Any document classified as Confidential or containing personally identifiable information (PII) subject to CCPA, HIPAA, or other US privacy regulations must never be shared via an anonymous link.
Classic email attachments are giving way to cloud links. When a user attaches a file from OneDrive or SharePoint, Outlook generates a sharing link.
OneDrive is each user's personal workspace — and it is often where the largest volume of authorized shadow IT accumulates. The sharing interface offers granular security options that should be actively used:
Admins can enforce global restrictions — for example, disabling "Anyone" links on OneDrive while leaving them available on SharePoint.
SharePoint structures team-level collaboration. External sharing works at two levels:
Governance risk: Without dedicated tooling, it is extremely difficult for a site owner to get a consolidated view of who accesses what — with a mix of site members and unique sharing links all in play.
Teams has become the central hub for external access.
Guest Access: The classic method for adding an external member to a team. The guest can access all channels (except private ones), associated SharePoint files, and chat.
Shared Channels (Teams Connect): This advanced B2B collaboration feature lets external users from other Microsoft 365 organizations participate in a specific channel only, without gaining access to the rest of the team.
Technical prerequisites:
Unlike classic Guest Access, Shared Channels create a dedicated SharePoint site for that channel only, independent of the main team site.
Storage architecture by Teams context:
Governance impact: This multi-silo architecture complicates backup, DLP, and retention strategies. Organizations should inventory dedicated channel sites via PowerShell to ensure full compliance policy coverage — particularly for HIPAA, CMMC, or other regulated data environments.
Securing external sharing does not mean blocking it — it means governing it. Here are the priority recommendations to roll out across your organization.
The "Anyone with the link" option must be the exception.
For any B2B collaboration:
A legitimate share at the start of a project becomes a security liability once the project ends. Data security depends on lifecycle management.
The IDECSI platform delivers a clear, consolidated view of all external access and sharing across Microsoft 365:
Despite Microsoft's ongoing improvements, the native Microsoft 365 interface remains fragmented. Users still lack a single console to see all their active shares across OneDrive, SharePoint, and Teams. That visibility gap makes it nearly impossible to hold employees accountable for their own sharing behavior.
The solution: equip employees with a tool like MyDataSecurity.
MyDataSecurity acts as a personal security dashboard for every user:
By giving data owners direct visibility into their own sharing activity, every employee becomes an active participant in the organization's security posture. That is the shift from reactive IT control to shared governance.
Securing external sharing no longer happens exclusively in the Microsoft 365 admin center. Technical policies — forced link expiration, domain restrictions, MFA — are the foundation of your defense, but they are not enough to keep pace with the volume and velocity of today's collaboration.
In 2026, the challenge for CIOs and CISOs is moving from a model of enforced control to one of shared governance. Data protection does not have to slow productivity — if it is made understandable for the people who create and share the data. By equipping users to see and clean up their own access, you dramatically reduce the security debt in your tenant without adding load to the IT team.
The goal is clear: keep business collaboration fluid while ensuring that every active external link is legitimate, secured, and necessary.
Ready to assess your organization's current Microsoft 365 exposure?
See how MyDataSecurity enables you to audit and remediate your collaborative environment — directly involving data owners in the process.
Recent articles
Subscribe to our newsletter and receive new contents every month
Our articles
These articles may
interest you