Microsoft 365 E3 vs E5: Full Security Comparison [2026]
To strengthen data security across Microsoft 365, IT and security teams need a clear picture of what each license tier actually delivers, and where the gaps remain.
Microsoft offers multiple license levels with varying security and compliance capabilities. The highest tier, Microsoft 365 E5, provides broad coverage with advanced analytics and risk assessment tools. For budget reasons, most organizations assign E5 to a limited VIP population (C-suite, security admins) while the rest of the workforce runs on E3. For users with minimal needs, E1 may be sufficient (occasional use, email-only access).
Given the critical priority of securing data and collaboration tools in M365, this article maps what E3 and E5 natively include, then identifies what third-party solutions like IDECSI add to close the remaining gaps.
Three use cases covered:
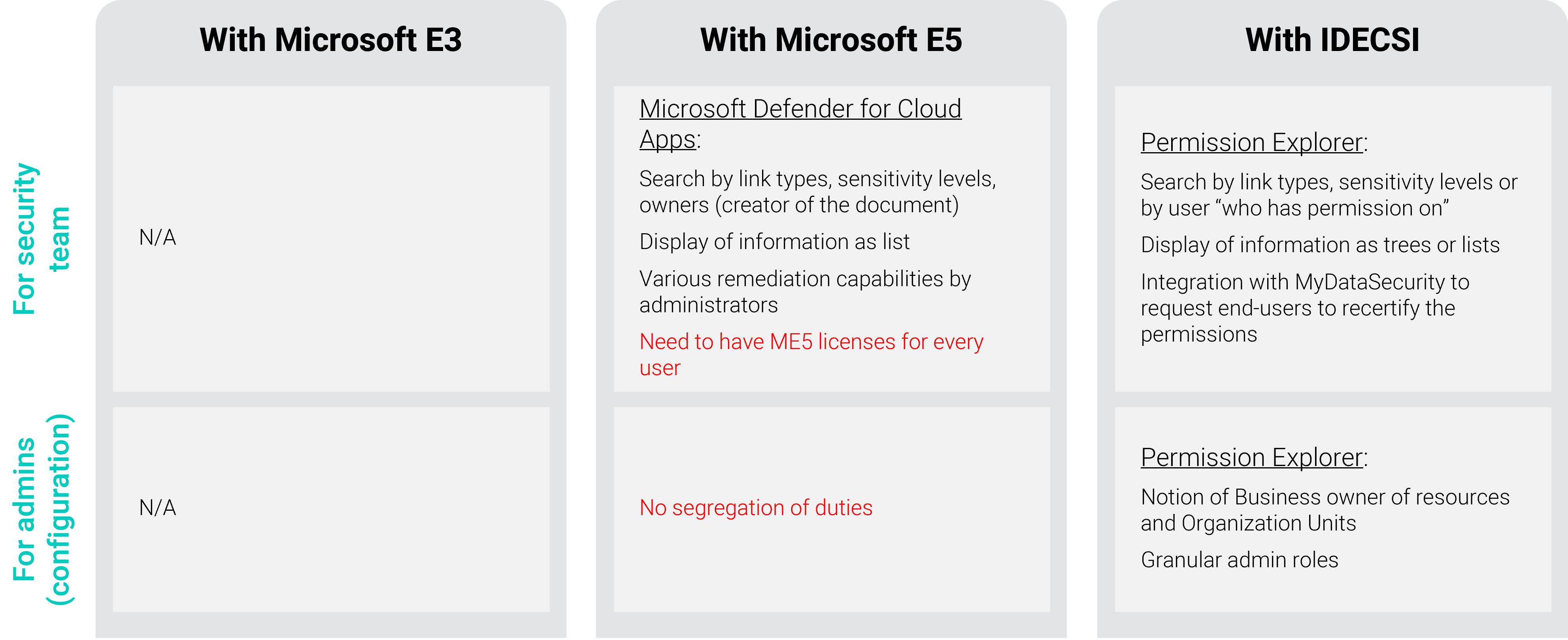
Permissions Auditing by Administrators
What Microsoft Provides for Permissions Auditing
Microsoft 365 E3
E3 offers no native mechanism for administrators or users to audit or control permissions at scale.
Microsoft 365 E5
E5 includes Microsoft Defender for Cloud Apps (formerly MCAS). Admins can:
- Search by link type, sensitivity label, or owner (defined as document creator)
- Apply remediation on permissions
Key limitations remain:
- Security groups are not expanded. All admins see the same level of information with no ability to segregate access by business unit, requiring a centralized compliance team.
- Visibility covers access events only, not user rights. Investigation is limited to internal users (guests excluded).
Permissions Auditing: The IDECSI Layer
IDECSI complements Microsoft's native offering with a dedicated admin analysis tool, Permission Explorer, that supports role-based granularity across organizational perimeters.
Permission Explorer delivers:
- Visualized rights, delegations, and access history for files, folders, and specific resources
- Cross-environment search (cloud and on-premises) by link type, sensitivity level, or user
- "Who has permission on what" queries, per user, per resource
- Structural analysis of permissions: inherited vs. direct, depth level, current access holders
Integrated with the MyDataSecurity user platform, IT teams can run rights review campaigns that engage data owners directly, asking them to validate or remediate permissions on their own data.

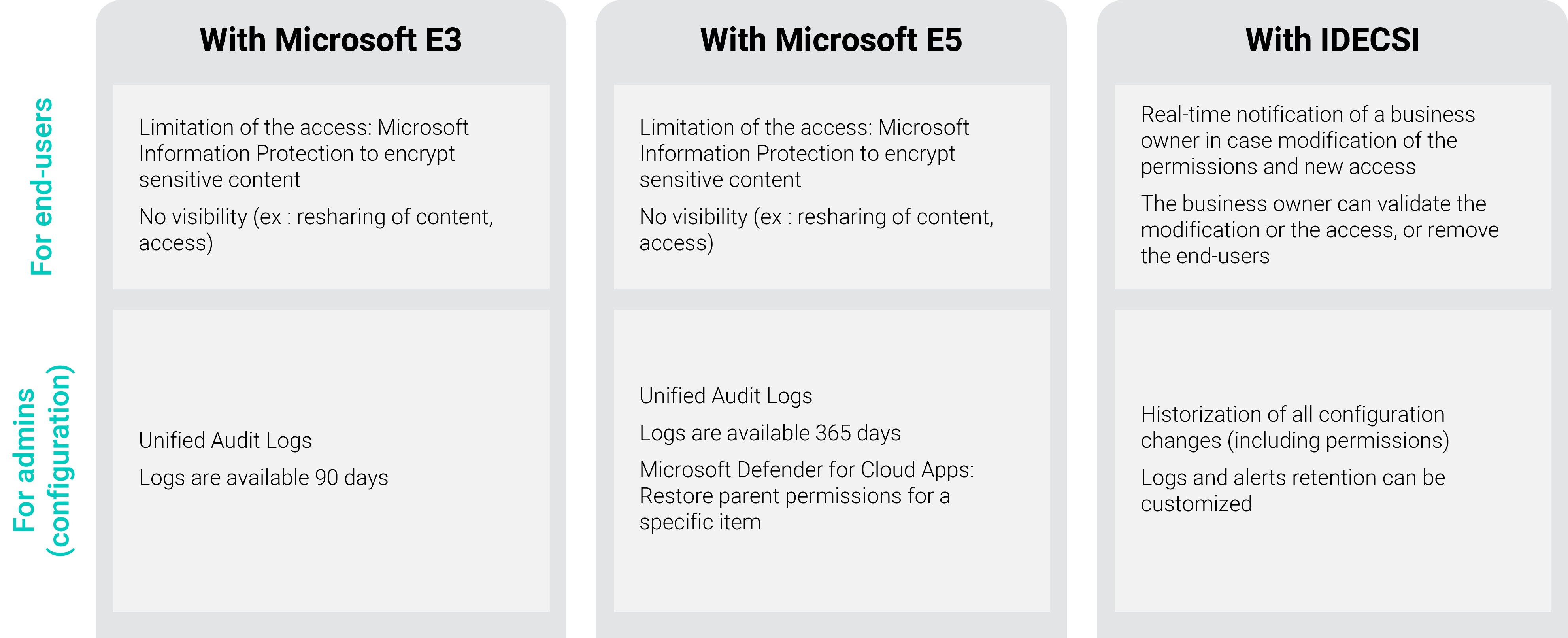
Monitoring and Alerts on Sensitive Data Access
What Microsoft Provides by License Tier
Microsoft 365 E3
Microsoft Purview (E3) gives admins access to the Unified Audit Log to track user and admin activity. Logs are retained for 180 days by default.
Admins can run manual audits to answer questions like:
- Who accessed a sensitive file?
- What actions were taken on a confidential document (shared, deleted, etc.)?
Users can apply Purview Information Protection (MIP) sensitivity labels to encrypt sensitive content and restrict access, based on internal classification policy.
Microsoft 365 E5
E5 extends audit log retention to one year. Admins also gain access to Defender for Cloud Apps, which enables:
- Restoring permission inheritance (removing unique permissions and reverting to parent folder/site settings)
- Workflow-based alerts to document or resource owners when behavior deviates from policy (e.g., anonymous sharing)
Admins can receive alerts when:
- A user shares sensitive data externally
- A user shares sensitive data in violation of company security policy
- A user exhibits abnormal behavior
By default, end users are not notified, but workflows can be configured to include them.
Sensitive Data Monitoring: The IDECSI Layer
IDECSI builds on Purview sensitivity labels to extend monitoring and data protection across the tenant.
For IT and security teams, IDECSI provides:
- A full data map organized by sensitivity label and exposure level
- Complete history of configuration changes (including permissions), with log retention
- Customizable alerts for policy changes, labeling actions, or sharing of sensitive data
IDECSI also engages data owners directly, adding a user-side monitoring layer:
- A "Points of Attention" view in each user's personal dashboard, filtered by classification level
- Real-time notifications to the data owner when permissions change, new access is granted, or abnormal behavior is detected
- One-click remediation : the owner can validate the change, block access, or remove specific users

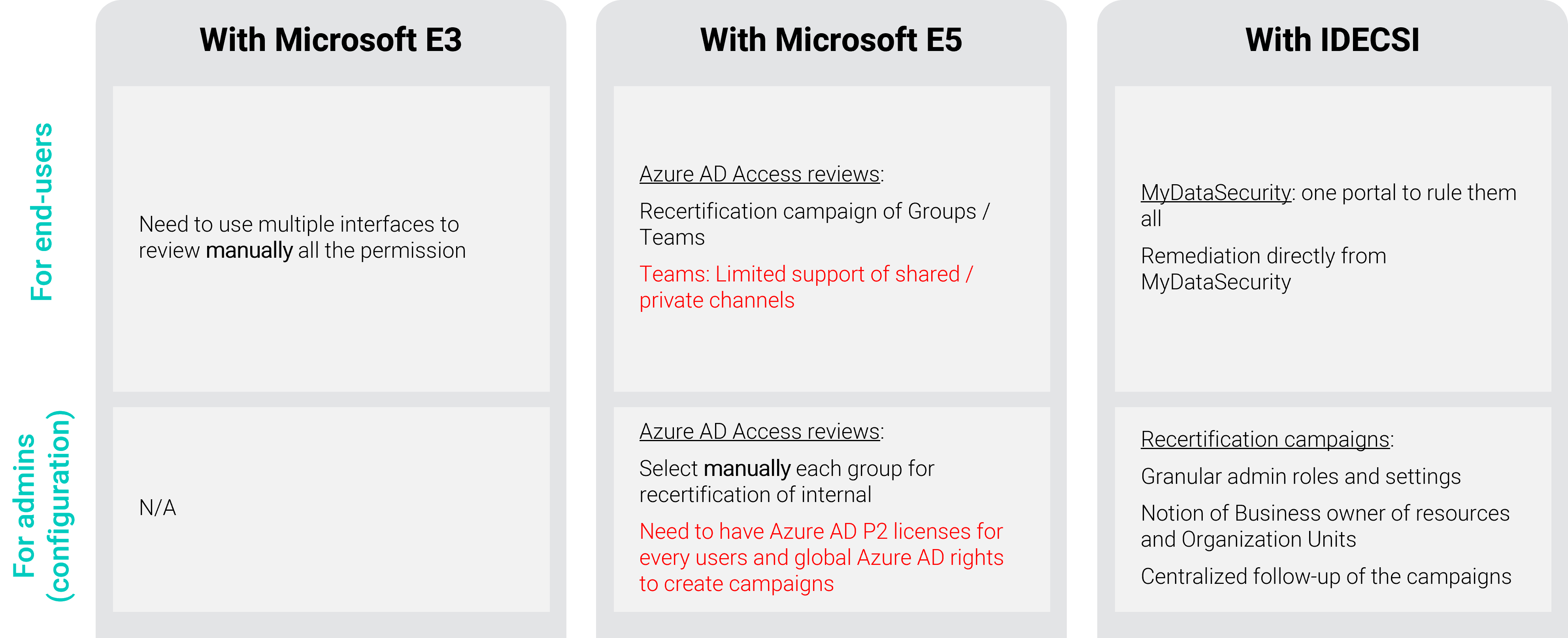
Access Rights Reviews in Microsoft 365
Access rights reviews are a core component of data protection. The goal: verify that user access rights match both company security policy and current job responsibilities.
Access Rights Reviews by License Tier
Microsoft 365 E3
E3 administrators have no dedicated tool for running large-scale access review campaigns. Users can perform reviews manually, but must navigate to each application individually and remove permissions file by file, a time-consuming, error-prone process.
Microsoft 365 E5
E5 includes Entra ID Access Reviews (part of Entra ID P2). Admins can monitor and manually recertify internal groups and launch campaigns targeting users.
Notes:
- A single license covers guest access reviews
- Review scope: all groups with guests, or group by group (manual selection or via API)
- Recertification campaigns apply to Microsoft 365 Groups: Teams or modern SharePoint
- The review covers group membership only — sharing links or permissions set outside of group membership (e.g., direct SharePoint permissions) are excluded
- After a campaign launches, group owners receive an email to review members. Shared channels are not included
- For other applications (OneDrive, Exchange), the process reverts to the same manual approach as E3
IDECSI Simplifies Access Rights Reviews in Microsoft 365
IDECSI developed a dedicated recertification platform, MyDataSecurity, designed to handle the volume and complexity of enterprise-scale rights reviews, and to maintain that security posture over time.
Administrators get a full campaign management interface with controls for:
- Targeting: global resources or specific scopes
- Duration and recurrence
- Automated reminders
- Customized email and notification templates
Campaign dashboards track user validations and remediations in real time.
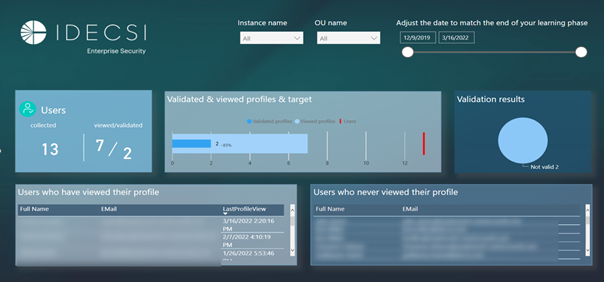
Each user gets a personal security dashboard to manage governance across their data — reviewing rights, access, and sharing from a single portal. During a campaign, users receive targeted notifications to recertify their permissions and can apply automatic remediation with one click.
IDECSI Extends Microsoft 365 Security Across All License Tiers
Microsoft 365 E5 bundles significant security and compliance capabilities, but it carries a substantial per-user cost. Most organizations run mixed environments, with E5 reserved for a subset of high-risk roles and E3 (or E1) covering the broader workforce.
IDECSI fills the gaps across both tiers. The platform adds five core functions to any M365 security stack: data collection and traceability, user-led rights reviews, admin-level control and audit, alerts and investigation, and consolidated reporting, covering cloud and on-premises environments.
Microsoft and IDECSI have jointly developed a security function mapping for Microsoft 365, giving organizations a clearer view of how to build a complete, optimized data protection program.
The key insight: even with E5, permissions sprawl, oversharing, and user-level data exposure remain unaddressed by native Microsoft tooling. IDECSI closes that gap by connecting IT visibility with direct user accountability, turning data governance from an IT burden into a shared, measurable responsibility.
FAQ
Q1: What is the main security difference between Microsoft 365 E3 and E5?
A1: Microsoft 365 E3 provides a solid baseline with core identity controls, device management, and standard compliance tools. E5 adds advanced threat protection across email, endpoints, identity, and cloud apps — including Defender for Cloud Apps, Entra ID P2 for privileged access management, and one-year audit log retention versus 180 days on E3. The gap is most significant for organizations with regulated data or a dedicated security operations function.
Q2: How do I audit permissions in Microsoft 365 without an E5 license?
A2: E3 does not include a native permissions audit tool for admins or users. The practical path is to complement E3 with a third-party solution that provides cross-environment permissions visibility, security-group expansion, and user-level rights analysis. Tools like IDECSI's Permission Explorer deliver this layer without requiring an E5 upgrade.
Q3: When does upgrading from E3 to E5 make financial sense?
A3: The upgrade from E3 to E5 costs roughly $21/user/month at standard 2026 US pricing. If your organization is already paying separately for Defender for Endpoint, Defender for Office 365 Plan 2, and a third-party SIEM, the bundled E5 cost is often lower than the sum of standalone licenses. The ROI case is strongest for security teams, legal/compliance roles, and organizations in regulated industries (healthcare, finance, government).
Q4: Does Microsoft 365 E5 satisfy HIPAA or NIST access review requirements?
A4: E5 includes Entra ID Access Reviews, which supports periodic recertification of group memberships. However, it does not cover sharing links or direct permissions set outside of group membership — a meaningful gap for HIPAA and NIST CSF access control requirements. Organizations handling protected health information or implementing NIST-aligned controls should evaluate whether additional tooling is needed to cover the full permissions surface.
Q5: What is the best way to manage data sharing risks in Microsoft 365 regardless of license tier?
A5: The most effective approach combines admin-level permissions visibility with direct user accountability. Native Microsoft tools provide monitoring and audit capabilities, but remediation still relies heavily on IT. Platforms like IDECSI's MyDataSecurity engage data owners directly, giving each user a personal dashboard to review, validate, and correct their own sharing permissions, reducing oversharing at scale without additional IT overhead. This user-led model has averaged 7 remediations per user across more than 1 million users on the platform.

